Multifactor authentication (MFA) is a security measure that is highly recommended to protect your accounts and sensitive information. MFA provides increased security by requesting additional verification information when members sign in, such as a code obtained from an authenticator app.
By configuring MFA, you can significantly enhance your organization’s security by preventing unauthorized access even if someone manages to obtain login credentials. Multifactor authentication is an essential, often mandatory, part of your organization’s security needs.
This article focuses on configuring MFA for ArcGIS logins only. For other supported login methods, please check with your identity provider.
About Organization Logins
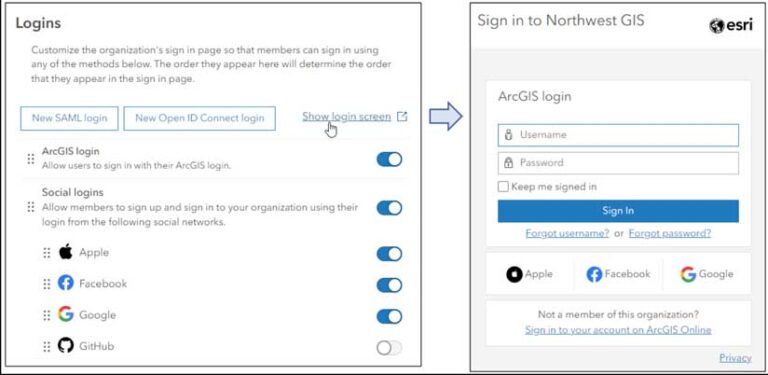
Your organization can be configured to allow members to sign in using a variety of methods, such as ArcGIS logins, Security Assertion Markup Language (SAML) logins, OpenID Connect logins, and social logins.
In the Logins section on the Security tab of your organization settings, you can set login options and reorder them. Click Show login screen to view the current settings.
Organization settings for MFA are only for ArcGIS logins and can only be configured by administrators or others with sufficient privileges. MFA for other methods other than ArcGIS logins must be configured via their respective identity providers.
For more information, see Configure security settings: Logins.
Enable MFA
You can enable MFA for your organization by choosing the Organization tab > Settings > Security. Scroll down to Multifactor authentication. If you have not done so already, when you toggle MFA, you will be prompted to designate at least two administrators who will receive email requests to troubleshoot members’ MFA issues. You can designate as many administrators as desired. This ensures that at larger organizations, especially those covering multiple time zones, administrative help will be available if needed.
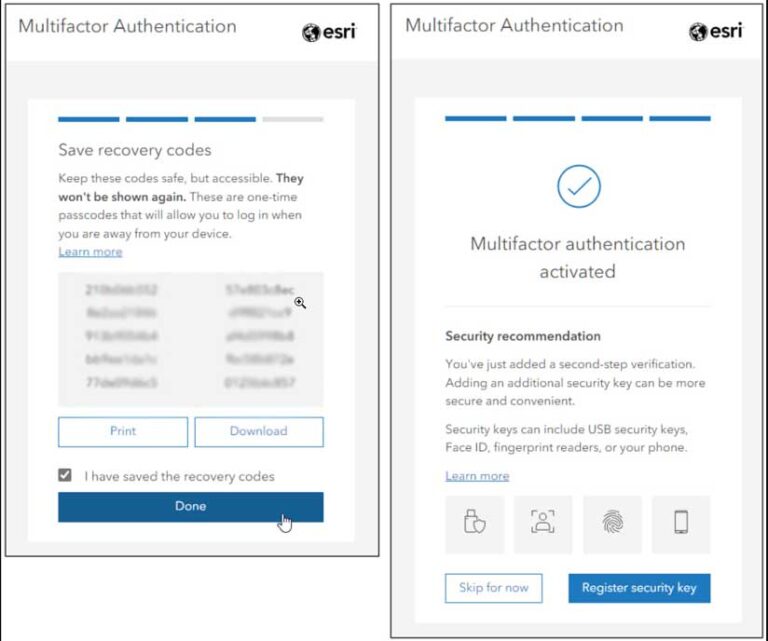
Once MFA has been enabled, you can optionally allow the use of recovery codes for organization members. Recovery codes are one-time-use codes that provide second-step verification when members lose access to their authenticator app or security keys.
Without these recovery codes, members must contact organization administrators to sign in if their configured authenticator app or security keys are unavailable. Members using recovery codes are responsible for properly storing the information.
Once Enable multifactor authentication for organization is toggled on, MFA is optional for members using ArcGIS logins unless enforced (see section below). MFA can be configured by individual organization members if they choose to do so. This setting can be found on the Security tab in the member profile settings. Members can click Enable to set up MFA for their account.
Once MFA has been enabled, administrators will see an MFA adoption status chart, showing how many members have set up multifactor authentication. This provides useful metrics for adoption and for moving forward with enforcement.

Enforcing Multifactor Authentication
MFA provides the highest level of security when it is enforced throughout your organization. Enforcement will require all members with ArcGIS logins to adopt MFA when signing in. Once you enable MFA you will see an option to enforce it, as well as an option to create a member exemption list that removes listed members from enforcement.
Click Enforce MFA to enforce MFA for ArcGIS logins. An information pane will display that underscores the considerations and immediate implications of MFA enforcement.
Things to Consider
All currently signed-in members using ArcGIS logins that have not configured MFA—whether they are administrators, field data collectors, or other members of your organization—will be forced out and will need to sign in again using MFA.
When members sign in again, they will be required to use a Time-based One-Time Password (TOTP) authenticator app, such as Okta Authenticator, Google Authenticator, Microsoft Authenticator, or another app to set up MFA. If an exemption list has been configured, additional charts will be displayed that let you track MFA adoption and show the status of required and exempt members.
Since this option circumvents multifactor authentication, it should be used only when special circumstances exist—for example, when a member needs additional time to procure and set up a device, is out in the field and does not have the means to set up MFA, or other similar situations.
Member Experience When MFA Is Enforced
When MFA is enforced, all members using ArcGIS logins will need to use MFA to sign in to the organization. Members currently signed in with ArcGIS logins who have not set up MFA will be signed out immediately. All members using ArcGIS logins who have not set up MFA will be guided through the setup process the next time they sign in and will need to have access to a TOTP authenticator app for completion.
Note that current activities, such as field data collection, map authoring, or analysis, may be interrupted. Best practices for ensuring minimal disruption of organization activities are listed in the best practices and considerations section below.
Those signing in for the first time after enforced MFA will be presented with a QR Code, used to configure the authenticator application. Use your camera via the authenticator app to complete the configuration. Once configured, the authenticator application can be used to generate the required code, providing secure sign-in access. After successfully entering the security code, if the option Allow use of recovery codes for members in the organization has been enabled, members signing in for the first time will be prompted to save the recovery codes (which they must acknowledge) and optionally register a security key.
Security keys can include USB devices, face recognition, a fingerprint, or other options. Security keys can be used as a second factor during authentication, following the first factor of a valid username and password. Members are highly encouraged to configure one or more security keys. Security keys are considered the best choice for preventing phishing attacks, while reducing the time for members to authenticate their identities.
Members can also go to the MFA section of their Security tab in their member profile settings to obtain recovery codes or register security keys for the second factor.
Best Practices and Considerations
When implementing MFA, test the waters. If you are unsure about the impacts of MFA across your organization, you can set it up without enforcing it. This gives members the option to try it out and the ability to provide feedback. You can gauge adoption via the MFA adoption chart. Once you’ve reached a threshold of adoption, you can move forward with enforcing multifactor authentication.
Plan ahead for multifactor authentication, especially if you will enforce it. Enforcing MFA will automatically sign out any members with ArcGIS logins who have not yet enabled multifactor authentication, which will interrupt ongoing work and processes including field data workflows and analysis workflows.
To avoid unwanted disruptions, you can temporarily add members to the MFA exemption list. Members may also be unfamiliar with how MFA works and need some time to install an authenticator app. Forward planning will minimize any confusion and interruptions.
Communicate Your Plans
Communicate in advance your intention to implement MFA and provide a target date. You can leverage the Information banner and Access notice settings to get the word out to members using ArcGIS logins. These settings are found on the Security tab of your organization settings.
Note that information banners are visible to anyone, including visitors to your site, so they may not be the best way to communicate these changes. Access notices, which are only shown when members sign in, may be the better choice. For more information on how to use both banners and access notices, read the blog post “Get the word out: Use information banners and access notices in your ArcGIS organization.”
Offer TOTP App Suggestions
A wide variety of TOTP authenticator apps are available. Organization members may be unfamiliar with the options, so coming up with suggestions (perhaps with guidance from your IT department) will ease the confusion.
Ensure the Highest Level of Security
Your reasons for implementing MFA are based on a need or the requirement to increase the security of your organization. With that in mind, enforcing MFA is the logical choice and so is encouraging members to use security keys. Ensuring compliance and best practices for members is a worthy goal when it comes to security. Adopting MFA is a significant step toward increased security, benefiting both users and organizations.
For more information, see these sections of the help documentation:
Sign in
Configure security settings
View your settings