Under construction…
Apologies, this blog article is being updated.

Please check back soon, this resource will be even better once we finish.
(By Bern Szukalski and Blake Stearman, ArcGIS Online development team)
This blog article was originally published on May 23, 2015, and has been updated.
As an administrator you want to keep your data and workflows secure, but also allow members of your organization the freedom to accomplish tasks efficiently. ArcGIS Online provides a number of security features to help protect your organization’s accounts and data.
This blog article is intended to be an overview of a few key aspects of ArcGIS Online account security that you can consider as an administrator. You will likely want to coordinate with your IT department for guidance on specific settings and options, plus consider additional settings not covered here. Besides these security features, it’s also essential for members to follow best practices for sharing, publishing content, and account security.

All settings below can be set by an administrator and are found in the Security tab of your organization settings.
Policies
Access and permissions
Allow anonymous access controls whether your organization home page can be viewed without needing to sign in. If your home page is intended as a destination where anyone can find useful maps, apps, or other information, you will want to allow anonymous access. If you intend to verify your organization, this setting must be enabled to allow anonymous access.
Tip: When anonymous access is enabled, your home page tabs and gallery should be configured to provide the best experience and impression for visitors. See Configure your home page navigation bar and galleries for more information.
Password Policy
Administrators may now alter the required password strength used to login to the organization.
Each organization has the default ArcGIS Online password policy requirements as its base level password security. But now administrators may alter that policy to require that passwords contain letters, upper and/or lowercase letters, numbers, special characters, as well as control the minimum number of characters used in the password.
In the Password Policy section found in the Security tab, click Update Password Policy to make the desired changes
Using Password Policy, you can specify password length, case sensitivity, and inclusion of numbers and special characters. You can also specify a rotation interval for your organization’s passwords, as well as enforce unique passwords over a configurable length of password history.
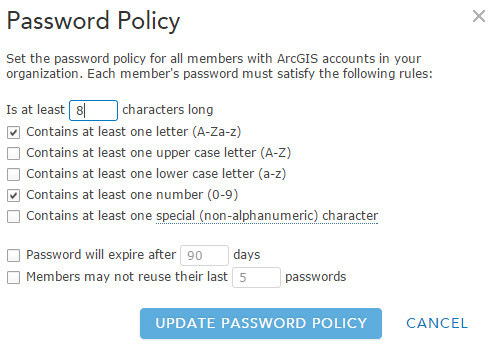
Once changes are saved, new passwords that are configured for users within the organization will follow the updated policy rules. Organization administrators can also reset passwords for members so that at their next log in they will be forced to specify a new password following the current password policy of the organization.
Multifactor Authentication
ArcGIS Online has implemented multifactor authentication as an additional configurable security option available to organizations. Administrators may specify that users enter a secondary security code from a mobile device in addition to their password, to further protect the security of their accounts. Settings for multifactor authentication can be found in the Security tab of your organization settings.
When configuring this option, a minimum of two administrators must be specified. Each will receive emails regarding any authentication issues with the organization. Having multiple administrators sharing this responsibility ensures that authentication issues within the organization can be dealt with in a timely manner, and that there is a backup in case one administrator is locked out (for example, if the device used for secondary authentication is lost).
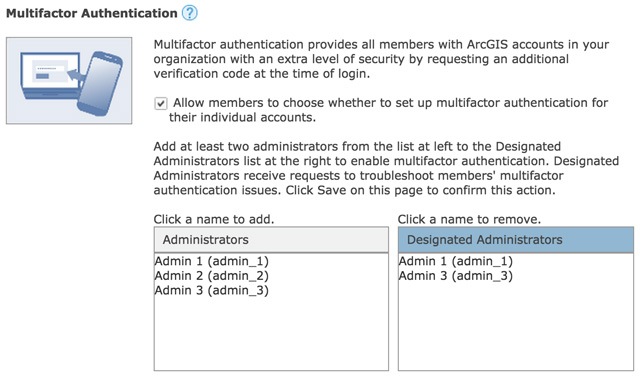
When multifactor authentication is enabled, administrators can view and sort by members currently configured to use it. Administrators can also reset the multifactor authentication configuration in case of a lost or forgotten mobile device.
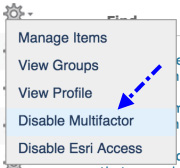
Organization members with ArcGIS accounts can configure or remove multifactor authentication on their account from their profile page. For member accounts managed by an enterprise identity provider it is assumed the enterprise identity provider would provide its own multifactor authentication solution, if one is desired.
For more information, see the following:

Commenting is not enabled for this article.