This blog post was contributed by Craig Cleveland, a Solution Engineer on the National Government Team in the Esri Washington, DC office.
Web AppBuilder for ArcGIS Developer Edition is the version of the app that you download and install on your local machine. You can easily create and deploy custom web apps within a “builder” user experience and it also enables you to work with custom widgets and themes when creating apps.
For those of you working with Web AppBuilder Developer Edition, you may have noticed the first time you browse to the site in a session you’re presented with a message from your web browser that looks something like this:
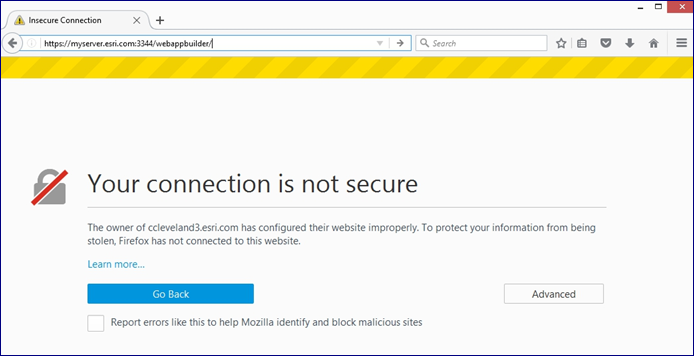 The reason this happens is because Web AppBuilder Developer Edition is using a self-signed certificate when communicating over the HTTPS protocol. FYI: trusted security certificates are used to create secure connections to a server via the Internet. Many of us will add the web browser exception, move on and not think about it again. However, this is not a security best practice, and in some environments can be a “showstopper”.
The reason this happens is because Web AppBuilder Developer Edition is using a self-signed certificate when communicating over the HTTPS protocol. FYI: trusted security certificates are used to create secure connections to a server via the Internet. Many of us will add the web browser exception, move on and not think about it again. However, this is not a security best practice, and in some environments can be a “showstopper”.
The ideal solution is to replace the self-signed certificate with a signed certificate from a trusted certificate authority (CA). Before we get into the specifics of how to accomplish this, if you’re unfamiliar with the details of SSL/TLS communication protocols here is a great overview provided by SSL Shopper.
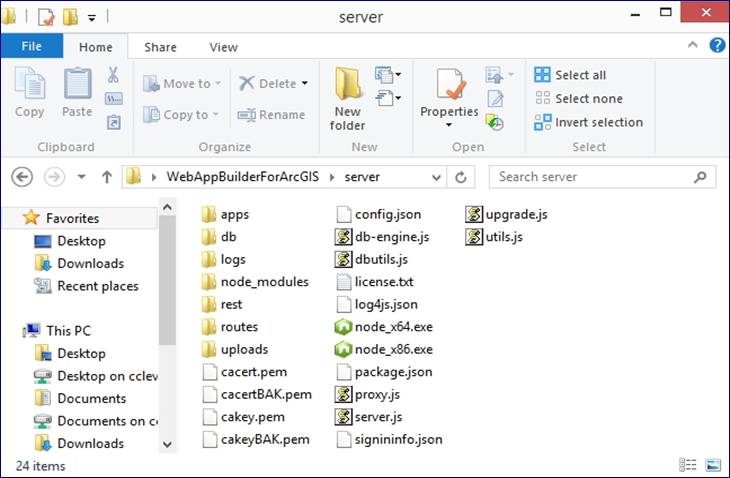
There are two files that need to be replaced in the Web AppBuilder Developer Edition server directory:
- cacert.pem, which is the public key for your server, and
- cakey.pem, which is the private key.
These files are generated during the installation of Web AppBuilder Developer Edition and reference your machine’s local hostname. Although there are multiple ways to accomplish this, in this blog we’ll explore one of the most common, which is to use openssl, a toolkit used to implement SSL protocols (Windows installer available here).
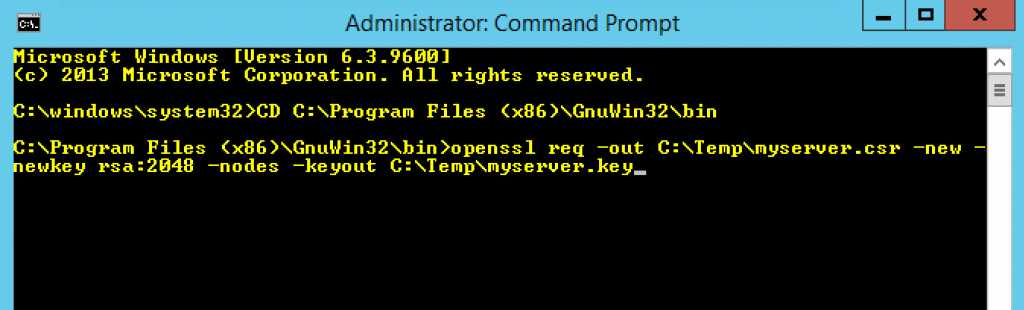
- The first step is to generate a new private key and Certificate Signing Request. Open a command prompt as administrator on your local machine by right clicking on Command Prompt in your Start Menu. Navigate using cd to the install location of openssl (e.g. C:Program Files (x86)GnuWin32bin) and run the following command, replacing “C:Tempmyserver” with your desired filename:
- The next step is to obtain a signed certificate from a trusted certificate authority. In this process you will present the .csr file created in the previous step to the certificate authority and have a signed server certificate returned to you. Depending on your environment the process to do this will vary, but here is a link that describes the process at a high level. If using a Windows machine with an IIS web server, you can follow these directions to generate a Domain CA-signed certificate. Generally, your IT team can be helpful in getting your CSR signed by a valid CA
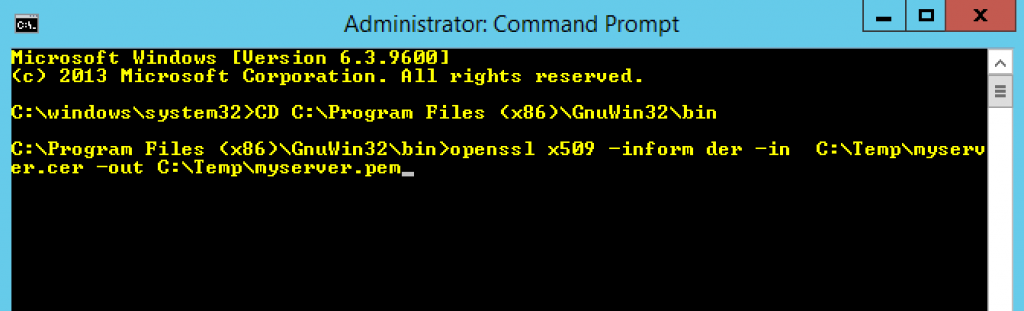
- The signed server certificate will most likely be returned to you in the form of a .cer file, and since we need it in .pem format we’ll need to run it through a conversion process using openssl. Once again open a command prompt as administrator, navigate to the install location of openssl (e.g. C:Program Files (x86)GnuWin32bin) and run the following command:
- Rename the myserver.key file created in Step 1 to myserver.pem.
- Replace the cacert.pem and cakey.pem files in the the Web AppBuilder Developer Edition server directory install with the two files created above. The files need to have the exact same names as the ones you’re replacing so make the following changes:
- The file created in step 3 (myserver.pem) will need to be renamed to cacert.pem, and the file created in step 1 (myserver.key) will need to be renamed cakey.pem.
- Once renamed, place them in the Web AppBuilder Developer Edition server directory.
Note: Be sure to back up the self-signed certs prior to replacing them with the ones created just in case!
On the next startup, Web AppBuilder Developer Edition will now be running with a signed server certificate, and the familiar green lock can be seen in the address bar of your web browser signifying you have a secure connection.
As a general best practice, it is always recommended to use CA certificates for your production server sites.
Article Discussion: