This blog post was contributed by Craig Cleveland, a Solution Engineer on the National Government Team in the Esri Washington, DC office.
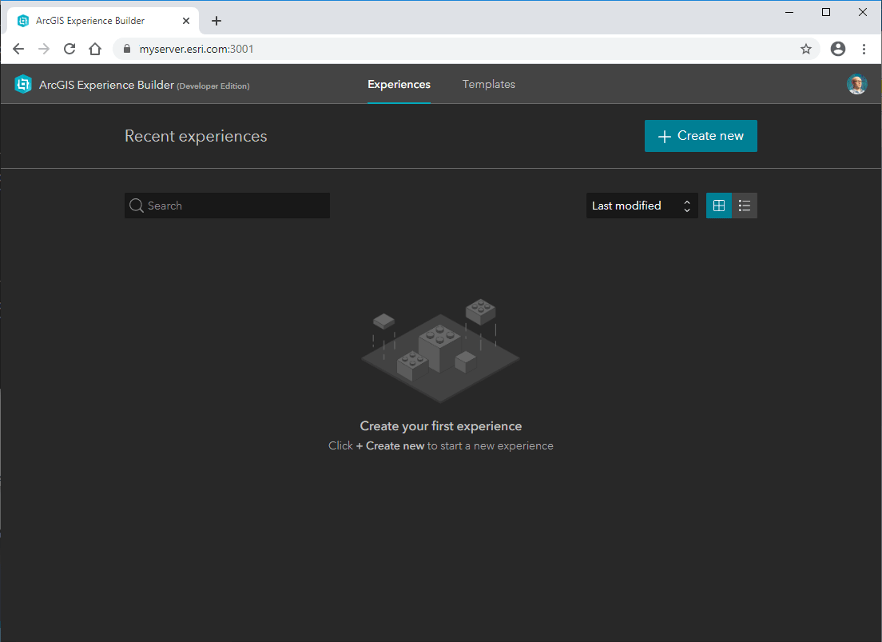
We delivered the initial release of the ArcGIS Experience Builder Developer Edition recently. For those of you that have deployed it already you may have noticed the first time you browse to the site you’re presented with a message from your browser that looks something like this:
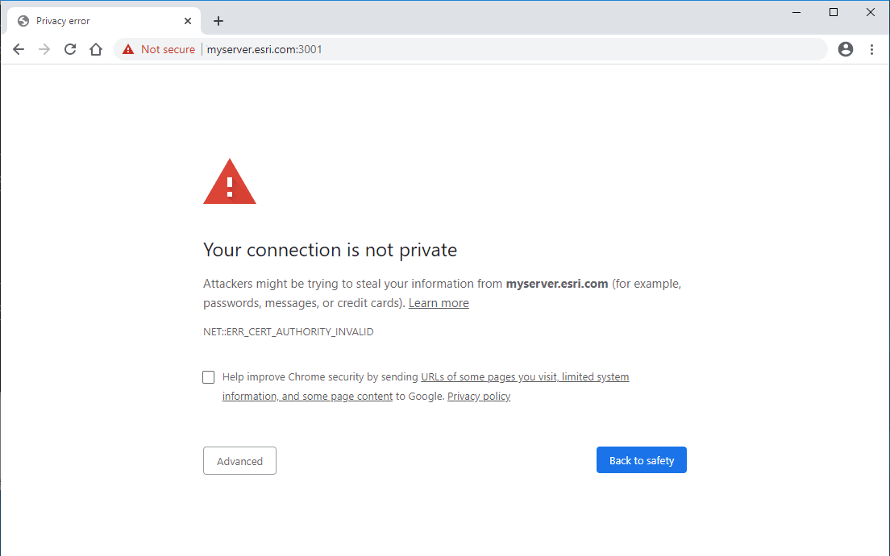
First, let’s dig into why you’re seeing this warning message from your browser. The browser is warning you because ArcGIS Experience Builder Developer Edition is using a self-signed certificate when communicating over https. Many ArcGIS components create self-signed certificates during the initial installation process so they can communicate via https immediately after installation. The easy thing to do is to make a browser exception, move on, and not think about it again. This is not a security best practice, however, and in many environments can be a downright showstopper. The ideal solution is to replace those self-signed certificates with signed certificates from a trusted certificate authority. All ArcGIS components allow for this to ensure the highest level of security when communicating over https. If you’re interested in more details about SSL here is a great overview provided by SSL Shopper.
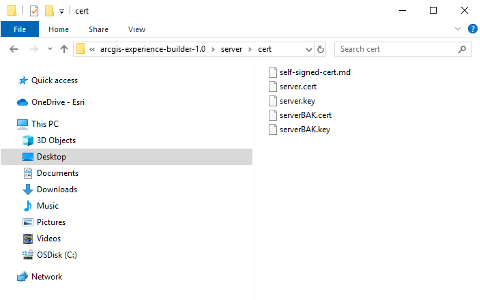
There are two files that need to be replaced in the cert directory of the ArcGIS Experience Builder Developer Edition install – server.cert, which is the public key for your server, and server.key, which is the private key. Although there are multiple ways to accomplish this, we’re going to explore one of the most common, which is to use openssl. Details on deploying openssl can be found here. Once it’s installed and configured you’re ready to begin.
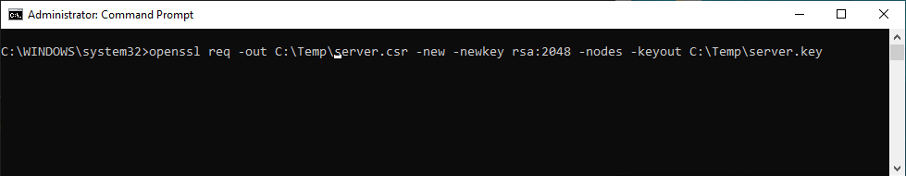
Step1: Generate a new private key and Certificate Signing Request
- Open a command prompt as administrator and run the following command:
openssl req -out C:\Temp\server.csr -new -newkey rsa:2048 -nodes -keyout C:\Temp\server.key
Step2: Obtain a signed certificate from a trusted certificate authority
- In this process you’ll present the .csr created in the previous step to the certificate authority and be returned a signed server certificate. Depending on your environment the process to do this will vary, but here is a link that describes it at a high level.
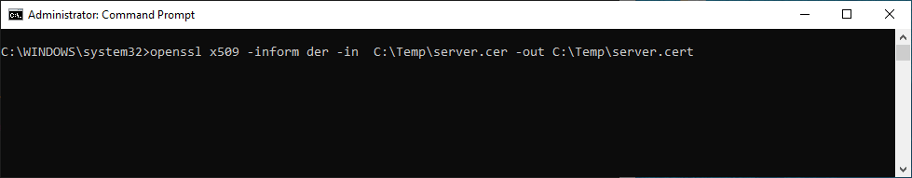
Step3: Convert the signed server certificate (if necessary)
- It’s likely the signed server certificate will be returned to you in the form of a binary .cer file, and since we need it in a base 64 encoded .cert format we’ll need to run it through a conversion process using openssl. Please note that if you’re able to get the certificate returned from the certificate authority in a base 64 encoded format this step is not required. Assuming it is, once again open a command prompt as administrator and run the following command:
openssl x509 -inform der -in C:\Temp\server.cer -out C:\Temp\server.cert
Step4: Replace the self-signed server.cert and server.key files
- Replace the files in the cert directory of the ArcGIS Experience Builder Developer Edition install (e.g. C: \arcgis-experience-builder-1.0\server\cert) with the ones created above.
Note: Be sure to back up the self-signed.
On the next startup ArcGIS Experience Builder Developer Edition will now be running with a signed server certificate, and the familiar lock can be seen in the address bar of your browser signifying you have a secure connection.

Article Discussion: